Our Insights
Innovative Ways - Satisfied Clientele
Innovative Ways - Satisfied Clientele

iFour Team - April 04, 2019
There are so many innovative technologies that made a vibrating impact in the digital world and Blockchain is being one of them. It is of no surprise that Blockchain has gained a spectacular traction in the market and impelled many blockchain software development companies to adopt in the development process. In this blog, we are going to discuss about Blockchain Consensus Algorithm: Proof of Stake Vs Proof of Work. A consensus algorithm is a process used to achieve agreement on a single data...

iFour Team - April 02, 2019
Blockchain technology has gained splendid traction in the current innovative world. It has achieved tremendous heights of success and making path-breaking impacts in different industry verticals. Underpinning with the cryptocurrencies like Ethereum, Bitcoin, it has changed the game of impossibility. The best part of this innovation is that it had shattered the hacking activities of the hackers. Being the best approach for security, many esteemed blockchain software development companies have...

iFour Team - March 27, 2019
Distributed systems in Blockchain are computing principles where two or more nodes work with each other in a coordinated fashion in order to achieve a common outcome. It is systemized in such a way that end users see it as a single logical platform. According to many Blockchain consulting companies the main challenge in distributed system design is coordination between nodes and fault tolerance. Here in this article we will learn distributed system in detail with current ecosystem. The...
iFour Team - March 20, 2019
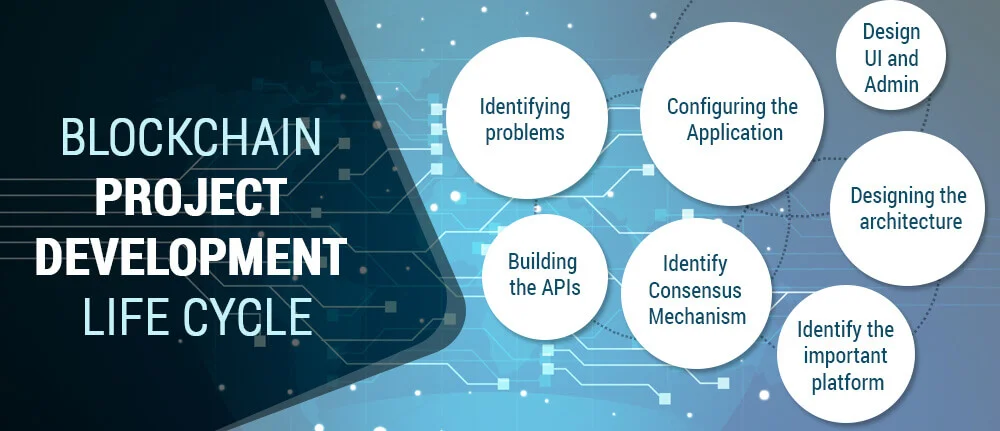
For the last few years, many innovative technologies have emerged that changed the outlook of the digital world. Blockchain is being one of those emerging technologies which got believed would make an impeccable impact on the digital market in the near future. Underpinning with cryptocurrencies like Bitcoin and Ethereum, it has closed the doors for hackers and thrashed their hacking activities. Because of such security, many esteemed Blockchain Software development companies have started to adopt...
iFour Team - March 18, 2019
Blockchain technologies top the lists of 2018’s hot trends. Many blockchain consulting companies already back their products with blockchain technologies. Competitors use different approaches to emphasizes different aspects and pitching them as features to their customers. So here we will know some particular aspects of Blockchain technologies that is “Consensus Mechanism”. A consensus is a fault trace Mechanism useful in Blockchain systems to achieve agreement single state of the network...